Currently Empty: $0.00
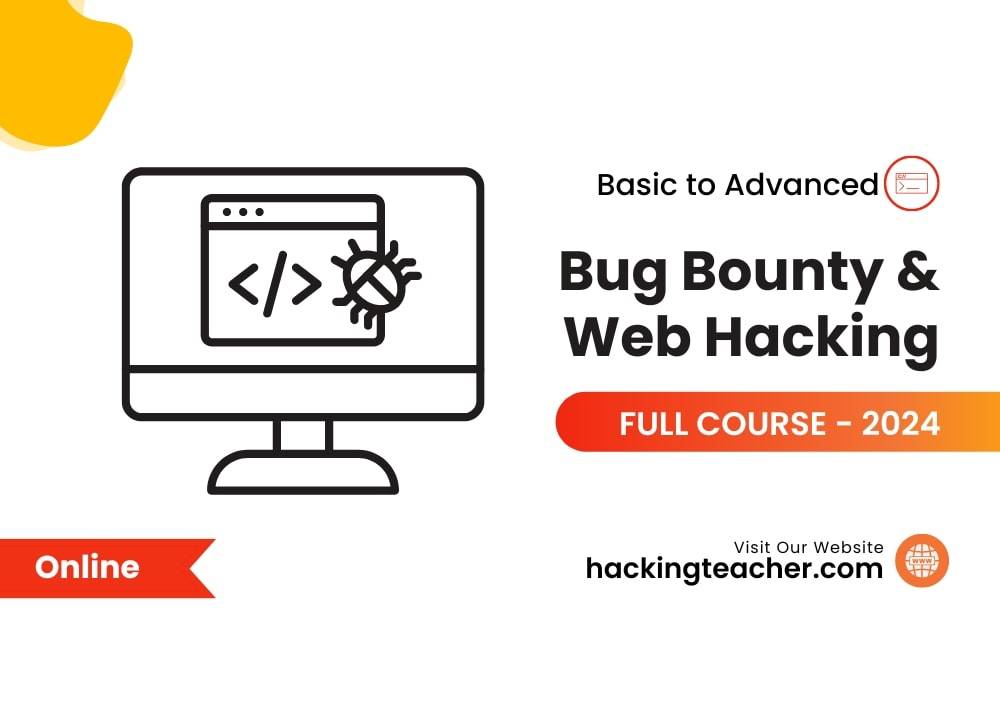
Bug Bounty & Web Hacking Course
48,570 Ratings
Welcome to the practical Bug Bounty & Web Hacking online course created by Hacking Teacher. This comprehensive course focuses on discovering and properly exploiting application vulnerabilities, providing a solid basis in Web Application Architecture, and delving into the critical OWASP Top 10. Participants in our online course will learn how to distinguish between Bug Bounty & Web Hacking Hunting, and Penetration Testing, as well as how to use critical tools such as Burp Suite in practical simulations. The curriculum covers sophisticated evasion strategies and how to overcome Web Application Firewalls (WAF), with an emphasis on ethical reporting and responsible disclosure. The course closes by assisting learners to strategically select Bug Bounty & Web Hacking programs and secure special invites, opening the road for a rewarding career in Bug Bounty and Web Hacking Hunting.
 Top Ranked Cyber Secuirty Course By HACKING TEACHER
Top Ranked Cyber Secuirty Course By HACKING TEACHER
Level Up for your Dream Jobs
Key Highlight of the Cyber Security Course
Industry-ready curriculum
Live expert metorship
2-week capstone project
Postagraduate certificate from Great Lakes
8 Hands on lab activites
CompTIA
India's Trusted Education Platform




Hacking Teacher Bug Bounty
Live course
Self Placed
Industry Expert
Academic Faculty
Cyberattacks can cause service disruptions, permanent loss of critical data, identity theft, and negative publicity for a corporation.
To reduce risks and losses, software companies actively scan for security flaws through bug bounty and web hacking programs. This is why we have developed the bug bounty and web hacking training course to produce experts in this paradigm of cyber security.
Sponsoring bug bounty and web hacking programs that encourage ethical hacking is one-way organizations may create a strong defense. A bug bounty and web hacking program is a monetary compensation offered to white hat hackers who correctly identify a security flaw that creates a vulnerability.
A vulnerability is a “weak spot” that allows black hat hackers—criminals who break into networks with malevolent intent—to obtain unauthorized access to a website, tool, or system.
A security weakness can often have disastrous consequences for a business. When bug bounty and web hacking training are combined with web penetration testing, which is an authorized simulated attack to evaluate security.
Make use of shared intelligence from global security experts. Identify issues that escaped the scrutiny of the internal security team’s pen testers and vulnerability scanners. Foster goodwill within the cybersecurity community prevent unanticipated losses.
Course Includes:
- Price:
$450.00$399.00
- Duration:1 months
- Language:English
- Certifications:Yes
| Training Modules | |||
| Chapter 01 - Hacking Pre-Requisites | Chapter 02 - Virtualization concepts | Chapter 03 - IP Address and Socket | |
| Chapter 04 - Networking Essentials | Chapter 05 - Wireless Fundamental | Chapter 06 - Basic Wireless Security | |
| Chapter 07 - Setup Window Firewall | Chapter 08 - Capture Network Data | Chapter 09 - Os Boot level concept | |
| Chapter 10 - Kali Linux Fundamental | Chapter 11 - Basic Linux Commands | Chapter 12 - Blacklisting IP Address | |
| Chapter 13 - Website Fundamental | Chapter 14 - Basic Website Design | Chapter 15 - Common HTML Design | |
| Chapter 16 - Setup own web server | Chapter 17 - HTTP Protocol Concept | Chapter 18 - DNS Globalize Concept | |
| Chapter 19 - CC secure Transaction | Chapter 20 - Basic Coding in Python | Chapter 21 - Blocking Internet Users | |
| Chapter 22 - ENcrypting data Folder | Chapter 23 - BIOS level authenticate | Chapter 24 - Securing a laptop Theft | |
| Chapter 25 - Designing own network | Chapter 26 - Remote control Servers | Chapter 27 - Over all Security Design | |
Instructor-led Cybersecurity Certification Course live online Training Schedule
Flexible batches for you
JULY 15th
WeekendSAT & SUN (4 Weeks)
9.00 PM to 12.00 AM (IST)
CLASS 1
JULY 15th
WeekendSAT & SUN (4 Weeks)
9.00 PM to 12.00 AM (IST)
CLASS 1
JULY 15th
WeekendSAT & SUN (4 Weeks)
9.00 PM to 12.00 AM (IST)
CLASS 1
10% OFF, Save
End in: 19 h : 10 m : 29 s
Secure Transaction

Talk to our Training advisor
Students Placed after completing One year Cyber Security Diploma




Our Advantage
| Parameter | Video Based Programs | Virtual Session Based Programs | StackRoute programs from NIT |
|---|---|---|---|
| Outcome Driven Learning | |||
| Practitioner Designed Assignments | |||
| Live Mentor-led Sessions | |||
| Overall skill development with >= 60% hands-on activities | |||
| Project portfolio in Git | |||
| Resume & Interview preparation | |||
| Placement Support with Verified Records | |||
| Acquire Day 1 Job-Ready Skills with GenAI Edge |
OUR INSTRUCTOR
Meet Out Expert Instructor

Sandip Sethi
Cyber security analyst
(4.8 Ratings)
OSCP | CRTP | CEH

Anima Doshi
Cyber Security Engineer
(4.9 Ratings)
OSCP | CRTP | CEH

Ankit Prabhakar
Security Administrator
(4.8 Ratings)
OSCP | CRTP | CEH
Cyber Security course in India
The course specializes in bug hunting within high-value Bug Bounty programs and web hacking, offering hands-on training tailored for security enthusiasts.
The course is suitable for beginners in cybersecurity, bug hunters, developers, and security professionals seeking practical skills in ethical hacking and bug identification.
Participants will learn ethical hacking techniques, penetration testing, securing Android apps, and identifying common vulnerabilities.
Through hands-on exercises, real-world case studies, and simulated bug hunting scenarios, participants gain practical experience and problem-solving skills.
Graduates can pursue roles as bug hunters, penetration testers, ethical hackers, security consultants, or application security specialists, enhancing their job prospects and performance.
Skill Covered
Kali Linux
Security and Risk
IoT Hacking
Cloud Computer
Cryptography
KPI
Footprinting
Vulnerability Analysis
System Hacking
Malware Threats
We focus on essential exploiting topics such as SQL Injection, Wireless Networks, IoT Hacking, Cloud Computing, social engineering, sniffing, and session hi jacking.




Our Global Outreach
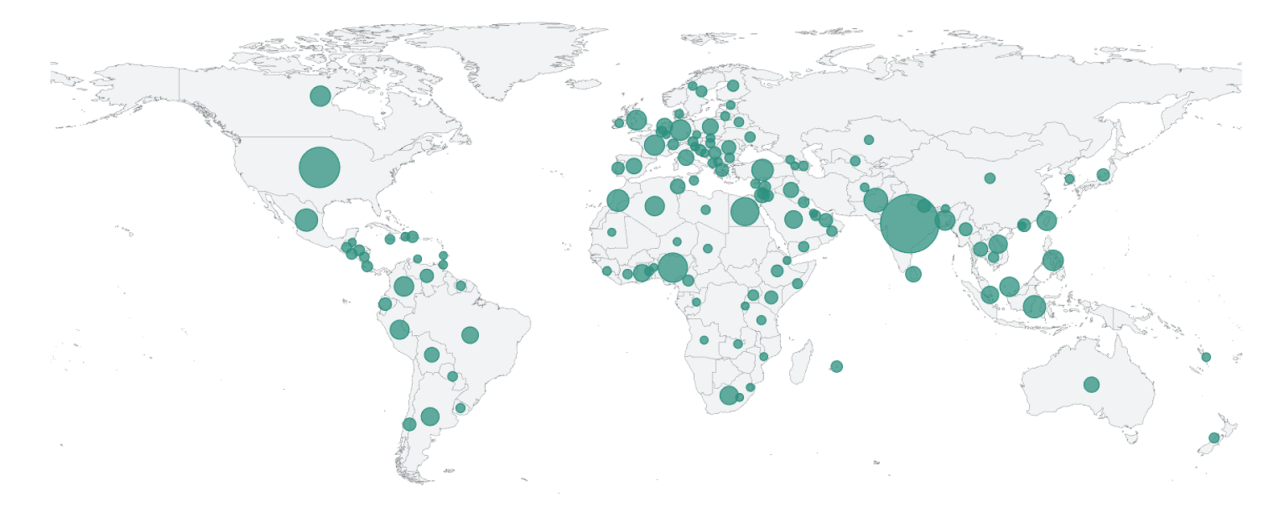
Students
0
+
Countries
0
+
Languages
0
+
HANDS-ON VIRTUAL LABS
What are Practice Labs?
There is a wide range of Bug Bounty and Web Hacking jobs available worldwide after completing our course, and India ranks higher than any other country in terms of offering the majority of the critical Bug Bounty and Web Hacking salaries in India related to various disciplines of cyber security.
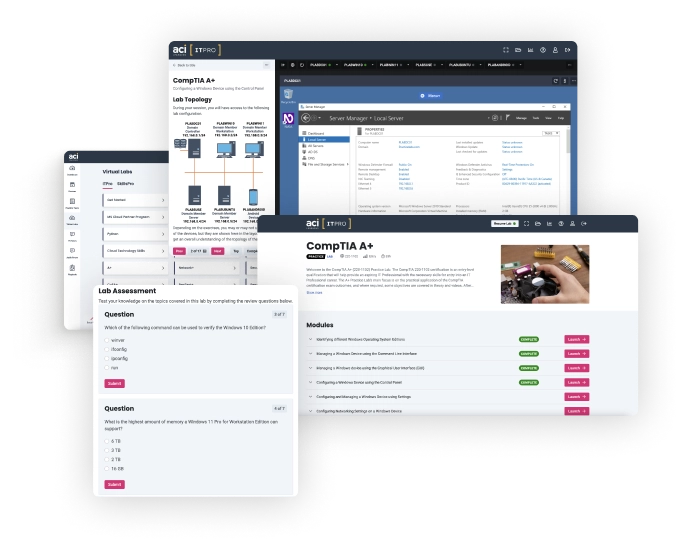
PROFESSIONAL LABSEnterprise Attack
Enterprise Attack
Simulation Training
Employees can practice sophisticated
penetration testing on enterprise infrastructure.

Hacking Teacher Cyber Security
Securing Tomorrow's Digital World









JOIN THE ALWAYS-ON TECH TRAINING SOLUTION
Be Bold . Train smart .
We, therefore welcome you to enroll for our Bug Bounty and Web Hacking course online as our trained professionals and experts are ready to impart you with knowledge to help you nurture your skill and produce a competitive guru capable of detecting and sealing any vulnerabilities associated with cyber security.

Course Reviews
(48,570 Review)

Kalini Mammen
Software Engineer at InnovateHub
“The Bug Bounty & Web Hacking course was an eye-opener! The instructor’s expertise and real-world examples provided invaluable insights into the world of cybersecurity. Highly recommend this course to anyone looking to sharpen their hacking skills.”

Alvi Rahman
Software Engineer at ByteBoost
“Thoroughly impressed with the Bug Bounty & Web Hacking course! The instructor’s practical approach and hands-on exercises helped me understand complex concepts with ease. This course is a must for anyone interested in ethical hacking.”

Nitya Gaba
Data Analysis at FreshCo
“The Bug Bounty & Web Hacking course was fantastic! The instructor’s knowledge and passion for cybersecurity were evident throughout the course. I feel much more equipped to tackle real-world hacking challenges after completing this course.”
Frequently Asked Questions
Our online courses are tailored to your specific needs, whether you are an experienced senior executive or a rookie leader.
- General Questions
- Regular Questions
- Advanced questions
What is ethical hacking and how is it used?
Ethical hacking is a hot topic in cyber security, producing ethical hackers to protect an organization's digital assets, which may contain critical or sensitive information about their clients and employees that cannot afford to fall into the wrong hands of an adversary attempting to steal them without any proactive measures.
How many months does a cyber security course last?
This varies from institute to institute. Many institutes provide their own certificate and diploma courses in cyber security, complete with self-developed curricula and training durations. In this regard, HackingTeacher, the best cyber security online training platform, provides world-class infosec education through its One-month and three-month cyber Security Diplomas, which are fully accredited by FutureSkills Prime, a MeitY-NASSCOM digital skilling initiative, and duly approved by the Governments.
What qualifications are required for cybersecurity training?
A person who is willing to start a full-fledged three-month cyber security diploma course from scratch does not require any prior knowledge of the subject. However, HackingTeacher's three-month Diploma in Cyber Security course is ideal for non-IT professionals with no prior expertise in IT security.
Which course is best for cyber security?
The three-month Diploma in Cyber Security Course is facilitated by HackingTeacher via a highly decorated training instructor in an extremely repressed environment through live project-based online training to mold our learners so that they blossom flourishingly.
Can I study cybersecurity for one month?
Yes, there is a specific One-month diploma in Information Security offered by many top-tier trainers and mentors with years of genuine experience in providing quality cybersecurity training by HackingTeacher that one can sincerely choose to begin an outstanding career in cyber security.
Which diploma is the best for cyber security?
The One-month and three-month Cyber Security Diploma courses offered by HackingTeacher's highly decorated and experienced training faculties are the best you can get for cyber security education at a low cost when compared to other cyber security online platforms.
Is hacking a decent career?
Yes, we can observe that there are hacking operations or cyber-attacks targeting every government or private sector entity. Almost every corporation needs ethical hackers to protect their digital assets from the prying eyes of black hat hackers operating from any remote place around the world.
Can I learn to hack myself?
Yes, there is plenty of stuff on YouTube where you may easily learn hacking tactics. However, it is insufficient or accumulated in such a way that you may obtain any useful outcomes from them.
On the other hand, HackingTeacher, the premier cyber security online training platform, provides a world-class ethical hacking course or a full-fledged three-month cyber security diploma course at extremely low prices that are difficult to find elsewhere.
Which cyber security certification is ideal for beginners?
The HackingTeacher three-month Cyber Security Diploma, which is taught and mentored by highly experienced information security professionals from the beginning to the advanced levels, is ideal for people who have no or little expertise with cybersecurity.
What training is necessary for cyber security?
Learners must receive sequential training from world-class cybersecurity specialists who are well-known around the world to master the foundations of cybersecurity from the ground up.
What are the eligibility criteria for cyber security?
A person with a basic understanding of IT systems and a valid 12th-grade certificate from a recognized board anywhere in the world is eligible for the HackingTeacher's three-month Diploma in Cyber Security Course, which is fully accredited by FutureSkills Prime, a MeitY - NASSCOM digital skilling initiative.
What is the best course for ethical hacking?
The Ethical Hacking Course from HackingTeacher is the finest option for studying ethical hacking concepts at a basic level.
Is cyber security extremely difficult?
Yes, you may say, because it comes into the middle category of touch courses. Furthermore, medical and engineering courses are at the top of the rankings, whereas arts and humanities courses are at the bottom of this difficult course rating.
Who may take the cyber security course?
A person who is interested in understanding the foundations of cyber security to work in the industry or start their own can complete this cyber security course in three months through HackingTeacher's one-month diploma courses.
Which course is the best for hacking?
The internationally recognized three-month Diploma in Cyber Security offered by HackingTeacher, a well-known cyber security online training platform, is the ideal option for learning ethical hacking from the outset.